The recent hacking of the government site: COMELEC.gov.ph leads to a lot of doubt if the agency is capable of conducting the computerized election securely. The 2nd attack that leads to the database leak that compromised information of the voters, added to this doubt. Damage have been done and it only proves that there’s a security issue with the website of the agency.
Here are some of the possible measures that they can implement to avoid future attacks and DDOS issues:
- Hide the version of the web server and the server side scripting language.
- Rewrite the URLs without the question mark (?) symbol to avoid possible SQL injection. But I guess they are already implemented some preventive measures before using this kind of URL structure.
- Use HTTPS (SSL) instead of the regular HTTP.
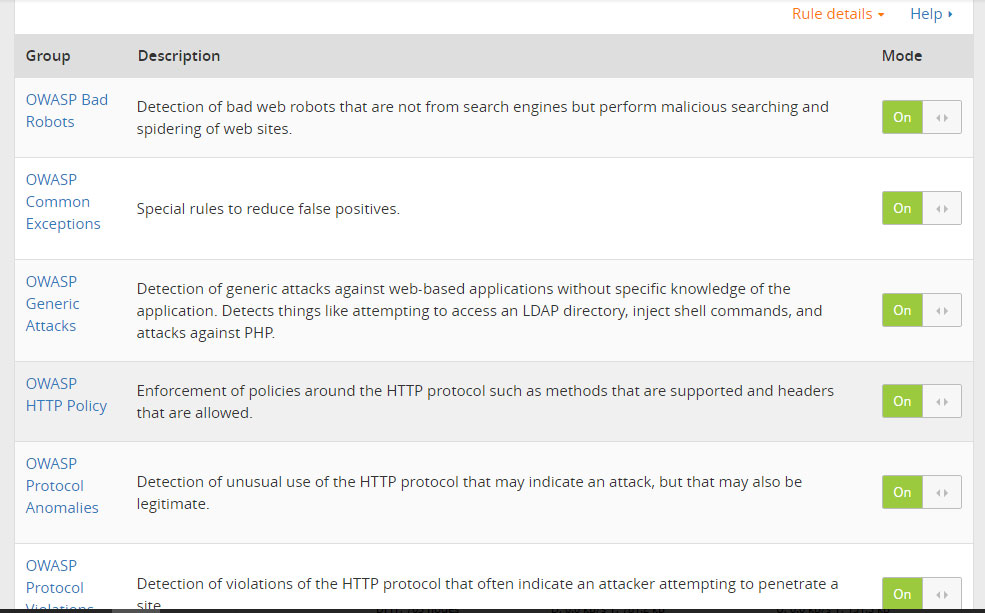
- Use Cloudflare as their CDN and firewall. They can implement an internal software firewall (using IPTables or the like) in their system closing all the ports and opening them only for Cloudflare to access (e.g. close port 80, 21, 25, etc then whitelist IPs of Cloudflare to access those ports). In that way, all traffic will undergo with the various security layer of Cloudflare before it will be served to users. Also with this method, the dedicated IP address of the site can be hidden from the eyeing attackers giving them a hard time to attack the site.
- Change the dedicated IP address of the site and hide it using the DNS service by Cloudflare. By using their DNS service, possible DNS spoofing can be avoided.
However, as the hacker movie “Who I Am?” says “NO SYSTEM IS SAFE!” but at least with these steps, you can mitigate the attacks that leads to a lot loses.
